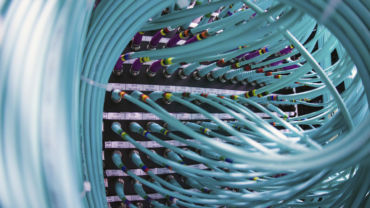
Image credit: REUTERS/Jason Lee
The topic of global cybersecurity will challenge each one of us. It is an unstable concoction of cultural norms and legal property rights patiently awaiting attention before it bursts. The overarching question is ‘how can legal organizations and overall society manage rising threats to the integrity of intellectual property (IP) whilst retaining and using information’? Add in the complexity that the global landscape is comprised of open societies, with freedoms and individuality, and close societies, of collectivism and oppression. The fundamentals of open society and IP rights—contrasted with closed societies and their misuse of IP through cyber threats will soon force change.
The Situation
The Council on Foreign Relations has been focusing recent seminars on emerging technology and cybersecurity as it relates to China and Russia. The thematic quintessence from the highest former administrators in the U.S. Intelligence Community is that the UK, Europe, and U.S. are under constant IP attack. They cited countless examples of nation states sending students and other professionals to the UK and U.S. with the sole intention of pilfering IP. Purportedly in one example, students at some of the best scientific universities are forced into this criminal role by their government. Their family, at home, is threatened if information from the student is not collected and given to the state. The majority of students have honest intentions in their travels—advancement of their own education and to enjoy the cultural exchange, but increasingly the U.S. Intelligence Community is alarmed at what they are finding. Commercial cyber espionage.
The cultural philosophies are starkly different, from one state to the next. The society of one state is open and the other closed. For example, pushing for individual’s governance of their own personal information manifested through General Data Protection Regulation—as with the European Union, while the other state created a ‘social credit’ score by ranking citizens based on their behaviour from data gathered by millions of facial recognition eyes in the sky. Both governments strive for rapid development in artificial intelligence, quantum computing, blockchain, and biotechnology. Governments develop these specialty areas in different ways. Eric Schmidt, former Google CEO, once said, “there will be two internets, one for China and one for the rest of the world”. The washing of information about the 1989 Tiananmen Square protests from every Chinese online forum and publication is cited as an example of the ‘other internet’. As a result, most teenagers in China have never heard of the protests which turned into a massacre.
Law firms as a collective serve as the largest holder of IP. As such, they are a top target for cyber espionage. The overarching laws are clear in the UK, and most often people abide by them. When there is conflict, legal process takes place and ultimately decisions are made, resulting in a final adjudication. What if no one paid attention to the decision? What if people did whatever they wanted, even though the IP for Flake candy bar is registered, China could copy it and sell it where ever they wished? This is the situation with the closed societies, and typically cybersecurity breeches are the means to an end for nation states looking to bolster their own companies.
The Dilemma
According to the U.S. Intelligence Community, the challenge is that closed societies are breaking into law firms and corporations, stealing IP and using it to build their own companies. The speed of these new companies built on the backs of stolen IP is phenomenal and will be much more difficult for those UK organizations to compete against.
Certainly, corporate espionage has been around since before cobblers competed in shoe-making. The difference is that open societies, by their nature, are now threatened by IP exploitation in the UK and US. Going forward and beyond sanctions, as the super powers of the world grow in strength and play by a different set of rules, law firms and corporations will likely need to map new ways how they protect their information and IP. The UK, U.S., and Europe will need to figure out how a society that plays by a clear set of rules competes against a society that can hack any law firm and use that information to illegally profit.